- Home » News » World News
Malware targets industrial controls and OPC servers

All three compromised companies develop software and appliances for industrial applications. They are based in Germany, Switzerland and Belgium. Two of them supply remote management software for industrial control systems, while the third develops industrial cameras and software.
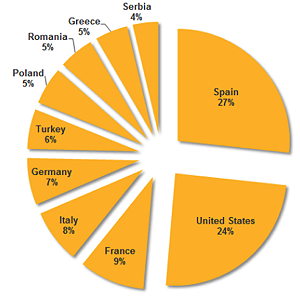
F-secure has also identified some of the targets of the malware attacks – all of which are associated with the development or use of industrial applications or machines. Most are located in Europe and include two German producers of industrial applications and machinery, and a machine-builder located in France.
According to a warning issued by the US Government’s Industrial Control Systems Cyber Emergency Response Team (ICS-CERT), Havex uses OPC (OLE for Process Control) to gather information about connected control systems resources in a network, including OPC tags, and sends this data back to the attackers. But ICS-CERT and F-secure haven’t found any evidence so far that the RAT has attempted to control or make changes to the connected hardware.
Havex only works with the original version of OPC – now known as OPC Classic – which was implemented using Microsoft’s CAM/DCOM technology. The latest version of OPC, called OPC Unified Architecture (UA), does not use CAM/DCOM and Havex does not appear to affect systems using this version.
According to F-Secure, the attackers behind Havex “are conducting industrial espionage using a clever method”.
“Trojanising ICS/Scada software installers is an effective method for gaining access to target systems, potentially even including critical infrastructure,” it points out.
According to Symantec, the Dragonfly group “displays all of the hallmarks of a state-sponsored operation, displaying a high degree of technical capability”. Based on the timings of the attacks, Symatec says it is likely that the attackers are based in Eastern Europe. It adds that the Havex RAT appears to be custom software, giving an indication of the capabilities and resources behind it.
“Dragonfly has targeted multiple organisations in the energy sector over a long period of time,” Symantec reports. “Its current main motive appear to be cyber-espionage, with potential for sabotage a definite secondary capability.”
ICS-CERT “strongly recommends” that organisations check their network logs for activity associated with the Dragonfly campaign. In particular, it recommends:
• enforcing strict access control lists and authentication protocols for network-level access to OPC clients and servers;
• considering the use of OPC tunnelling technologies to avoid exposure of any legacy DCOM-based OPC services;
• ensuring that the HTTP server enforces proper authentication and encryption of the OPC communications for both clients and servers, when using OPC .NET-based communications; and
• applying the OPC Security specification, where possible.