- Home » News » World News
ICS vulnerability discoveries soar by 110% in four years

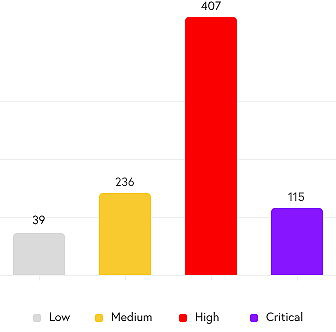
The number of cyber-vulnerabilities discovered in industrial control systems (ICSs) soared by 110% over the past four years, with a 25% increase (to 797) in the second half of 2021 alone, compared to the previous six months, according to new research from the security company, Claroty. Almost all (87%) of the vulnerabilities were rated as “low complexity”, meaning they don’t need special conditions and that attackers exploiting them could expect to be successful every time.
In its fourth Biannual ICS Risk & Vulnerability Report, Claroty suggests that the figures reflect a heightened awareness of the issue and a shift of security research towards OT (operational technology) environments
More than half (53%) of ICS vulnerabilities now involve remote code execution, followed by denial-of-service conditions (42%), bypassing protection mechanisms (37%), and allowing attackers to read application data (33%). Almost two thirds (63%) can be exploited remotely through a network attack vector, indicating that the need for secure remote access – which accelerated because of the Covid-19 pandemic – is here to stay.
Most vulnerabilities (70%) can be exploited without needing special privileges, and 64% need no user interaction.
The report finds that ICS vulnerabilities are expanding beyond operational technology (OT) to the extended Internet of Things, with 34% of those discovered in the second half of 2021 affecting IoT, medical and IT assets. Claroty suggests that organisations will respond by merging their OT, IT, and IoT activities under single security management systems. It adds that asset owners and operators need “a thorough snapshot” of their environments to manage vulnerabilities and reduce their exposure.
“As more cyber-physical systems become connected, accessibility to these networks from the Internet and the cloud requires defenders to have timely, useful vulnerability information to inform risk decisions,” says Claroty’s vice-president of research, Amir Preminger. “The increase in digital transformation, combined with converged ICS and IT infrastructure, enables researchers to expand their work beyond operational technology (OT), to the Extended IoT (XIoT).
“High-profile cyber-incidents in 2H 2021 – such as the Tardigrade malware, the Log4j vulnerability and the ransomware attack on New Cooperative – show the fragility of these networks, stressing the need for security research community collaboration to discover and disclose new vulnerabilities.”
Although the number of vulnerabilities discovered by automation vendors themselves grew by 76% over the past four years, half were found by third parties – mostly cybersecurity companies. Claroty says this demonstrates a maturing industry and discipline around vulnerability research, with vendors allocating more resources to the security of their products.
The most commonly recommended step for mitigating the effects of vulnerabilities is network segmentation (suggested for 21% of vulnerabilities), followed by protection against ransomware, phishing and spam (15%) and restricting traffic (13%).
The report is available as a free download.
Claroty: Twitter LinkedIn Facebook